OT/ICS Vulnerability Management for Power Grids
Security regulations for critical systems, such as the EU NIS directive and NERC-CIP, and other cybersecurity frameworks and standards stipulate vulnerability management as a key aspect of any cybersecurity program for the power grid. By mapping publicly known vulnerabilities to your system infrastructure, you can determine and implement an appropriate response based on risk assessment. Thus, threats to the network are identified and the integrity of your system is ensured.
Always remember: You can only protect, what you see. The database – which our security analysts have created – shows you all the vulnerabilities which are relevant to your system. The more information you have about each asset, the more accurate your detection, analysis, and prioritization will be.
Risk prevention is a process that starts with identifying your status quo: your assets, your associated vulnerabilities, and your infrastructure attack vectors. However, you also need to implement proper security protection/prevention measures. A continuous monitoring of the power system traffic with an IDS is necessary. If your risk assessment detects any malicious activity, an accurate response is needed, before recovering and quickly bringing the network back to the normal state.
Did you know: All our cybersecurity solutions can be found on brand-new website. Explore our products and solutions now: omicroncybersecurity.com
Take a look
Expert recommends
StationGuard Solution
Our IDS StationGuard and its central management system GridOps work perfectly together: while GridOps provides the management interface for StationGuard’s sensors across the grid, StationGuard collects all the data and analyzes it.
Our Products
StationGuard allows robust asset inventory management with comprehensive and rich data per asset. It meticulously collects all asset details but only displays vulnerabilities which are relevant to you. This is crucial to successful vulnerability management.
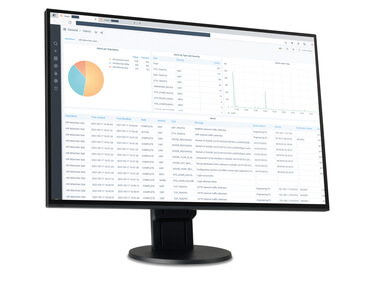
GridOps is a component of StationGuard that provides additional management and features, such as grid-level asset inventory, alert dashboard, sensor management, centralized user management, vulnerability management, and reporting.

Our cybersecurity products have a new home
Explore OMICRON‘s vulnerability management alongside our comprehensive cybersecurity portfolio, including intrustion detection, asset inventory, functional monitoring, and assessment and engineering services on our brand-new website!
Many Threats, One Solution
Control systems often use legacy equipment and software not updated with security patches. The patching requires these systems to be taken offline for maintenance, which is costly and disrupts critical operations. The risk of falling prey to attackers and ransomware increases over time.

The problem with security advisories
Security advisories for protection, control or network devices warn of such risks to the power grid. Unfortunately, many vulnerability disclosures are imprecise and lack relevant information and comparing security advisories to actual devices in protection and automation systems is challenging. You need to know the exact device type, module configuration, and firmware version to ascertain if a vulnerability applies to your fleet of IEDs and network equipment. You also need to determine if the affected services are used in your network and whether they have been exposed or not.

Information is the most important asset
Our StationGuard Solution was developed to take care of most of these tasks for you. Our security analysts created a database of known vulnerabilities for power grid automation which offers complete information. This database is also linked to an asset type database for identifying device types. Backed up by the most precise inventory management, our solution displays all the vulnerabilities which are relevant to your system. The more information you have about each asset, the more accurate your vulnerability analysis and reaction to threats will be.

Why do you need an exhaustive asset inventory list?
You can only protect what you see! Every network consists of an abundance of different assets, your asset inventory. To protect them against threats, you need to know about them first. This inventory of software and hardware used in your network contains all identified assets, it shows whether they are up-to-date or not, and enables you to manage and protect them from threats, such as malware, ransomware or ghost assets. This grants you the freedom to manage your critical infrastructure system with over- and insight.
Improve Your Security Risk Assessment with a comprehensive Vulnerability Management
Our StationGuard Solution enables a holistic approach to the essential security risk assessment for the benefit of your system security. Ensuring the availability of critical services is the goal. Therefore, our solution delivers insight into both cybersecurity aspects and functional aspects of the automation system and network. It aims to reveal security risks, such as attack surfaces, vulnerabilities, but also functional problems in the network or the automation devices. It also establishes an asset inventory to provide full visibility of the OT components and documents them.
Read on to learn why we highly recommend a holistic security assessment aided by our StationGuard Solution:

Security risk assessment – what are my benefits?
GridOps helps identify the most significant security risks (such as vulnerabilities) and allows your team to prioritize remediation efforts. The vulnerability management dashboard outlines the potential risks associated with your automation and control devices. Eventually, you will learn how you can minimize security incidents by complying with various laws, regulations, and standards.

Functional security monitoring for engineers and IT specialists
Our StationGuard Solution not only benefits IT security officers, but also protection and SCADA engineers. You will be able to monitor the grid via our intrusion detection system and, at the same time, also supervise the correct function of the automation system. Both aspects are related to cybersecurity, because configuration changes or device malfunctions could also be indicators for a cyber incident.

Threat detection – OT security is all about availability
The sensitive nature of the devices in utility automation systems requires security measures to not influence the real-time behavior and correct function of the devices.
Thus, GridOps' threat detection is designed to passively gather asset information from engineering files, spreadsheets and passive network observation. Protection and control engineers can optionally use our well-proven tools for active device interrogation to get the most recent configuration information about a device. This information is then compared to our purpose-built asset type and vulnerability database to detect relevant risks to your system.

Informed asset scanning – uncover potential zero-day exploits
Whilst discovering all asset information and the status of your network, StationGuard, additionally, monitors the correctness and timeliness of the messages on the network. This ensures not only the detection of vulnerabilities in these devices, but also the detection of exploitation of yet unknown zero-day vulnerabilities in power grids.
Benefits of this Solution

Watch for vulnerabilities as they emerge

Intelligent scanning for OT vulnerabilities

Visibility to stakeholders